All articles containing the tag [
Capacity Planning
]-
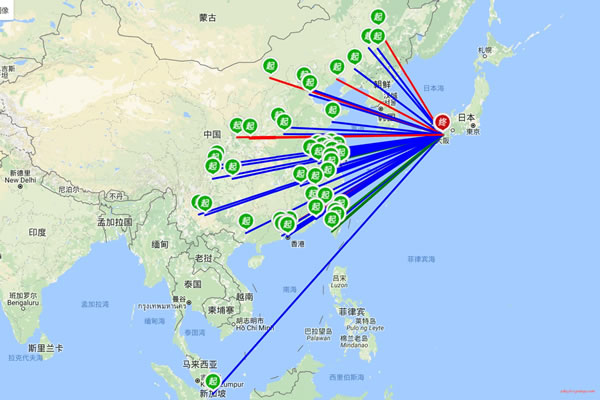
Step-by-step Explanation Of The Japanese Cloud Server Purchasing Process, Configuration Selection And Network Settings
step-by-step explanation of the japanese cloud server purchase process and common configuration choices and network settings, covering practical suggestions such as computer room selection, instance specifications, storage solutions, bandwidth and public network settings, security policies, high availability and backup, and performance monitoring.
japanese cloud server purchase process configuration selection network settings bandwidth security computer room selection backup monitoring -
How To Adjust The Configuration Of Cloud Virtual Machines In Cambodia Based On Traffic Forecasts To Reduce Waste
This guide explains how to adjust the configuration of Cloud Virtual Machines in Cambodia based on traffic forecasts. It covers aspects such as data collection, prediction models, auto-scaling, as well as recommendations for optimizing resource allocation and costs. These measures help reduce waste of resources and enhance the user experience.
Cambodian cloud servers traffic forecasting server configuration cloud resource optimization cost savings GEO optimization -
How To Adjust The Configuration Of Cloud Virtual Machines In Cambodia Based On Traffic Forecasts To Reduce Waste
This guide explains how to adjust the configuration of Cloud Virtual Machines in Cambodia based on traffic forecasts. It covers aspects such as data collection, prediction models, auto-scaling, as well as recommendations for optimizing resource allocation and costs. These measures help reduce waste of resources and enhance the user experience.
Cambodian cloud servers traffic forecasting server configuration cloud resource optimization cost savings GEO optimization -
Sharing The Best Practices Of Traffic Monitoring And Anomaly Detection For Long-term Use Of Native Ip In Taiwan
share the best practices of traffic monitoring and anomaly detection in long-term use of native ip taiwan, covering key indicators, collection methods, real-time monitoring, alarm mechanisms, compliance and automated optimization suggestions.
native ip taiwan traffic monitoring anomaly detection long-term use best practices network security operation and maintenance -
Practical Guide: What Is The Use Of Hong Kong Server Hosting? Application Cases In Coping With Bandwidth Peaks
this practical guide introduces the specific role and configuration points of hong kong server hosting in dealing with bandwidth peaks, including monitoring, elastic expansion, load balancing and case analysis, to help stabilize the response to traffic peaks.
hong kong server hosting bandwidth peak peak response practical guide application cases bandwidth elasticity load balancing -
Node Monitoring And Alarm Practices Ensure Long-term Healthy Operation Of Thailand Vps Nodes
this article introduces the monitoring and alarming practices of vps nodes in thailand, including key indicators, threshold strategies, alarm channels, automated recovery and common fault handling, to help nodes run healthily for a long time.
thailand vps node monitoring alarms long-term healthy operation network monitoring performance monitoring vps maintenance -
Full Analysis Of Process Costs And Compliance Requirements For Running A Server In Cambodia
comprehensive analysis of the process, cost structure and compliance requirements for setting up servers in cambodia, covering site selection, deployment, network, licensing and compliance risks and savings strategies. it is suitable for enterprises and individuals who are preparing to set up servers in cambodia.
cambodia server process cost compliance data center bandwidth localization filing -
From An Operations Perspective: Automatic Scaling And Alerting Solutions For High-security Cloud Servers In The United States
An analysis of the automatic scaling and alerting mechanisms for high-security cloud servers in the United States from an operations perspective, covering practical approaches and recommendations regarding traffic analysis, trigger policies, preheating and cooling processes, alert classification, and noise reduction. Suitable for applications that require protection against external traffic and high availability.
High-security cloud servers in the United States automatic scaling alarm systems operations and maintenance DDoS protection high availability auto-scaling monitoring -
This Technical Requirements List Outlines The Connection And Monitoring Specifications Prepared For The Hong Kong Cloud Hosting Data Center Proxy
This document outlines the technical requirements for access and monitoring solutions designed for Hong Kong-based cloud hosting data centers. It covers key aspects such as network connectivity, bandwidth redundancy, physical access, power supply infrastructure, permission management, performance monitoring, and log auditing, facilitating compliant implementation and operational maintenance.
Technical Requirements List for Monitoring Access via Proxy in Hong Kong Cloud Hosting Data Centers: Network Bandwidth Redundancy Security Log Monitoring and Alarm Functions